What Are RFID-Blocking Wallets and How Do They Work?
Are you on the lookout for a new wallet? Then you’ve probably come across wallets that claim to have RFID blocking technology. RFID technology is a relatively new notion in the industry, and this article will explain what it is and how you may create your RFID wallet. We recently walked you through how to test your wallet’s RFID blocking capacity as well as how to protect your credit cards and other NFC or RFID-capable objects in your wallet. RFID is a novel technology that uses electromagnetic fields to monitor and identify things via tags.
An RFID system consists of two parts: a tag and a reader. A label can be passive or powered by batteries. The title contains information that reads using a two-radio transmitter-receiver reader. The passive tag relays the data utilizing the reader’s radio wave energy, whereas battery-powered tags need a battery supply. The data from the label is sent to an RFID computer system after the reader has decoded it.
What are RFID wallets, and how do they work?
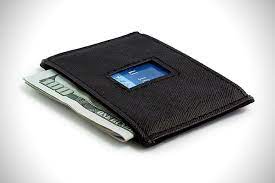
Wallet options used to be straightforward. Bifold, trifold, or clutch—more pockets, fewer pockets; leather or synthetic—are all possibilities. However, if you go to Sky Mall on your next journey, you’ll see a new and perhaps perplexing option: Blocking RFID. RFID-blocking wallets and sleeves, such as this one from Swiss Alpine and Buxton, promise to do more than manage your cards and cash. They claim to protect your personal information from cybercriminals. Are they effective and necessary? Under some theoretical situations, they could execute their job, at least to some extent. However, this does not imply that you require one.
RFID wallets
RFID wallets make to protect you from a specific type of electronic pick pocketing known as RFID skimming. Some credit cards, passports, and driver’s licences now have inbuilt radio frequency identification chips, causing worry. When triggered by an RFID reader, these chips transmit particular types of information wirelessly, allowing you to verify your identity or perform a transaction without having to swipe your card. Anyone with an RFID reader can turn on the chips and read whatever data they mean to send. They can even do it without your knowing if they’re sneaky.
Over the years, hackers have made news by demonstrating how a portable RFID scanner can “skim” sensitive data off people’s cards from a distance of several feet. Your passport might reveal your name and country of origin. More ominously, RFID skimmers have captured whole credit card numbers from the pockets of passers-by in certain rallies. RFID wallets make to block RFID signals from your cards, making them more challenging to read from afar.
Few things work as well as wrapping your cards in aluminium foil if you’re looking for maximum effectiveness. What’s less obvious is if RFID skimming is indeed a problem. Despite the excitement around the potential risk, there have been few, if any, cases of real RFID skimming crimes. This technology also facilitates our personal life! RFID chips assist in speeding up the process of having a passport examined when travelling, paying tolls instantly, and facilitating contactless credit card payment.
Unfortunately, thieves are resourceful and have devised methods to exploit this cutting-edge technological innovation. The approach appears to be significantly more prevalent among security researchers than among thieves. For a good reason: stealing people’s money and data is a lot easier and more successful. While early RFID payment systems may have communicated sensitive data such as card numbers without encryption, major credit card companies say this is no longer the case.
Their RFID chips now broadcast a one-time code for each transaction, so a determined thief would be able to make a single purchase by recording and reproducing the signal he picks up from a particular card at best. Even if that happened, most credit card issuers’ policies would exclude the cardholder from liability for the fraudulent transaction. From the standpoint of the thief, it’s a lot of effort for a small reward.




